I heard a story recently that might be true. The younger employees of a large international company had started to use Google Calendar for listing company events, and they started entering upcoming conference call-in information. Some of them set the "share" feature to "on." As a result, some private conference calls were attended by outsiders who, to be charitable, should never have been invited.
As social media and social networking become more visible we're bound to hear more stories like this. More likely than not, they'll be used as cautionary tales by those opposing social media or social networking.
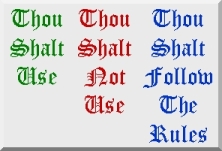
In my opinion, this type of thing can be avoided by implementing and promoting common sense rules. For example, don't post sensitive company, membership, or customer information in places where it's likely to leak out into the wrong hands.
The problem with this approach is that, increasingly, the barriers between internal and external systems are becoming increasingly blurred. So how is one to tell whether or not the system being used is one that is really secure from prying eyes?
This is an area where I think the IT department has to be involved. I don't mean by acting as a traffic cop, I mean as an educator and trainer. People who use technology as a normal part of doing business need some understanding of how it operates and how to control it. I don't mean that people need to understand how things operate "under the hood," but I do mean they need to understand the basic "rules of the road." Here are some examples:
- If the organization uses a remotely hosted application to manage customer or product data or processes, make sure people understand what happens when they are not connected to the network and how to deal with network outages.
- If the organization uses any type of collaborative tool or system, make sure people understand the manner in which access is controlled. For example, does a file owner have absolute authority over access, or can partners authorize others to have access?
- Use common sense when it comes to posting personal opinions and comments about other people, even within the context of a closed group.
It's not unreasonable for employees to be educated about such matters. Managing complexity is something we use technology to help us with all the time. Consider, for example, how a large insurance company has to accommodate the different regulatory rules for different states, or how a large utility must take into account different pricing and public access requirements of different regulatory jurisdictions. Call center representatives receive constant training on how to respond to different inquiries and how to use the different resources and technologies available to them to respond to inquiries.
As social media and social networking become increasingly popular methods for employees to interact inside and outside the firewall, rules will need to be established. For those rules to be understood and applied, though, some basic understanding of how software, networks, and communications system operate will be required. Given the rapid changes in these areas, the involvement of the IT department in promoting such understanding seems reasonable.